A unique product which combines holography and cryptography in a new way. Once designed for a specific purpose, the tag will contain a series of optically steganographic regions which will only respond to a readout software and reveal text or numerical information about the embodiment they are protecting. Due to the fact that mimicry destroys the unique optical footprint of the software readable parts of the tag, faked tags do not respond to the reader with correct information hence this generation of our nano-optical security solutions can protect the secured embodiment with utmost degree of security.
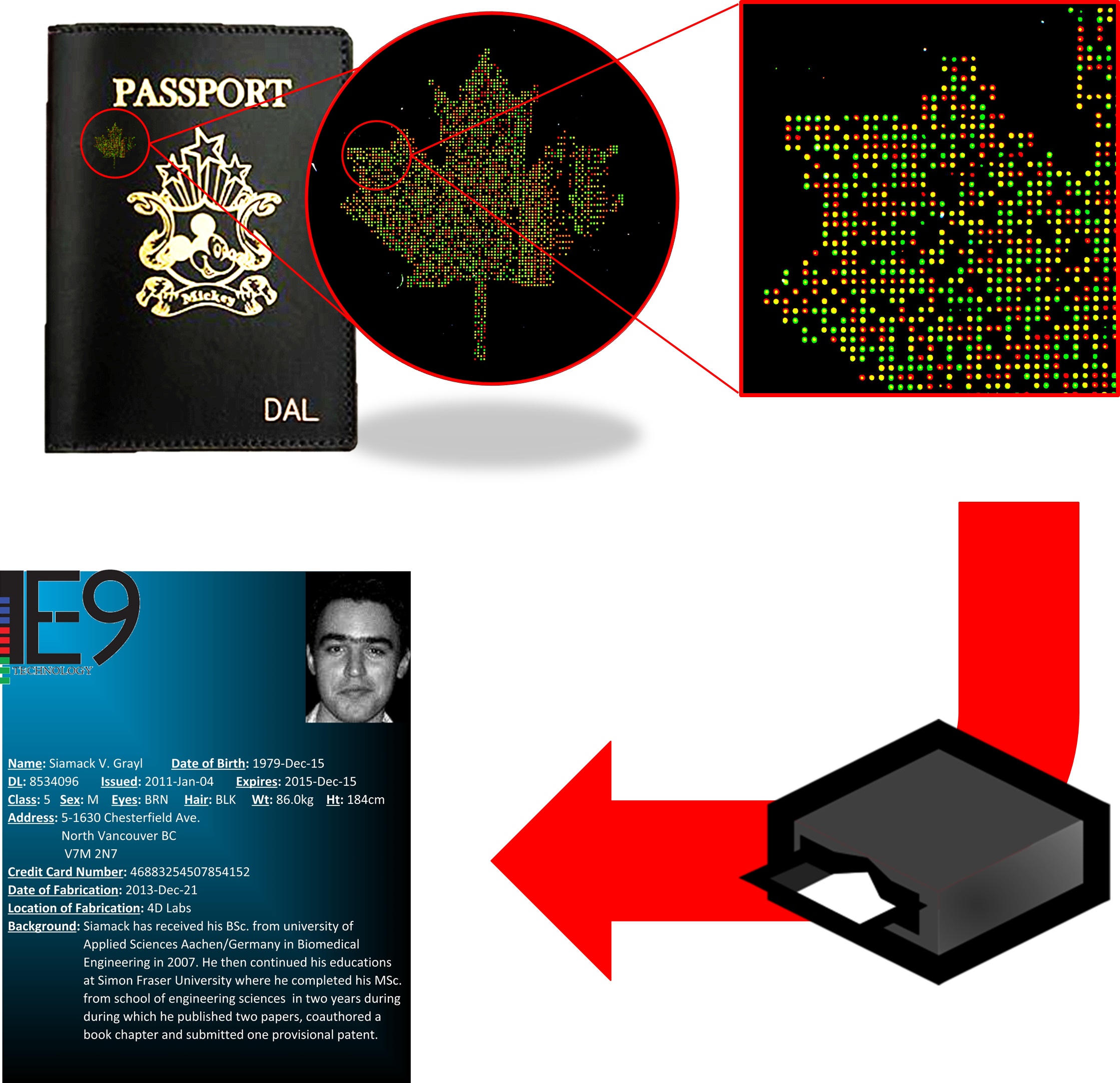
Figure 2. The cryptogram technology allows for embedded optical tags such as one shown up in the figure. Since the tag is incorporated into the ID documents material and contains optically encrypted data, a replication of both the tag bearer document and the tag itself both will fail the reader machine’s authentication process.

